Remote Desktop Access GPO
This project shows how I configured a Group Policy Object (GPO) to enable Remote Desktop Protocol (RDP) only for authenticated domain users and devices. The goal is to allow remote management while keeping access limited to trusted accounts inside the domain.
Objective
Enable RDP across domain-joined computers while restricting access so only authenticated users and approved domain devices can connect.
GPO Configuration Steps
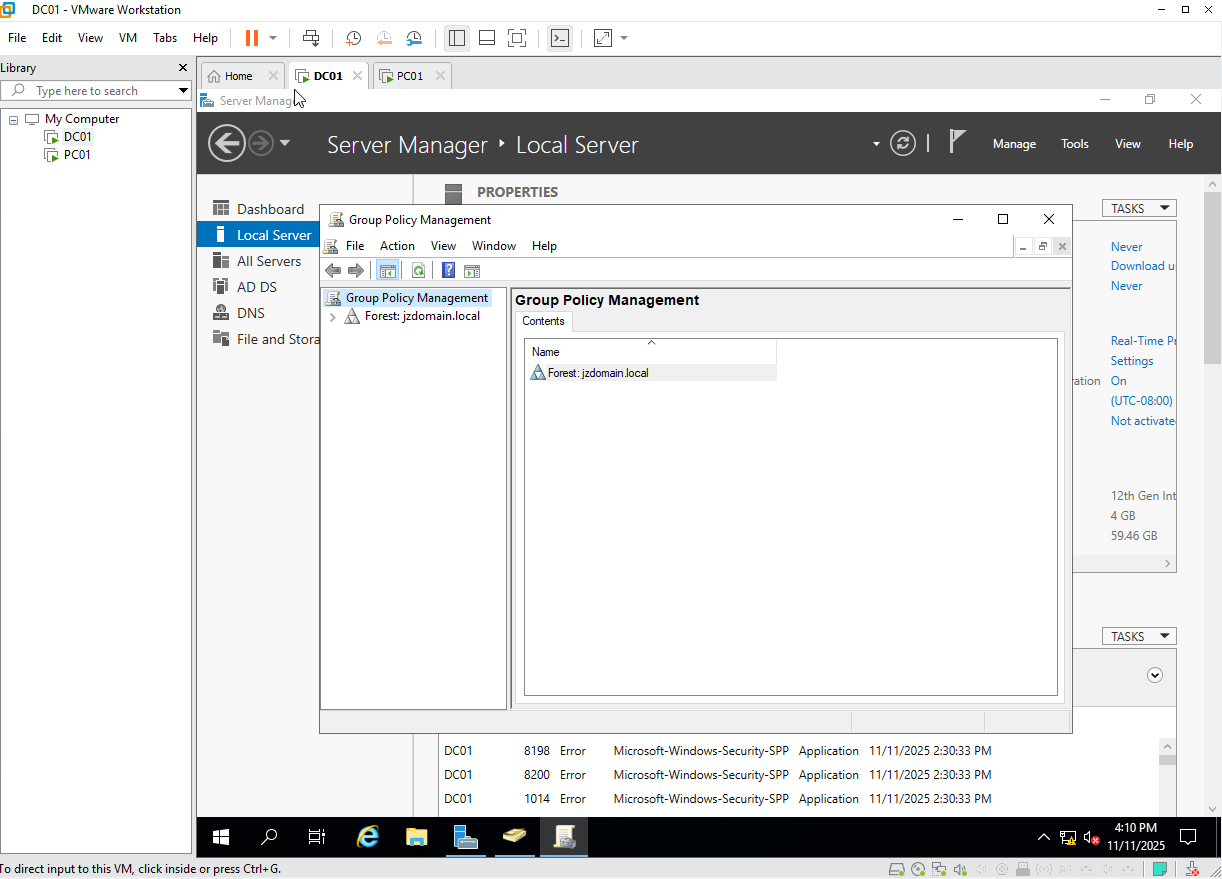
1. Open Group Policy Management Console
I started by opening the Group Policy Management Console (GPMC) on the Domain Controller. This is where domain-wide GPOs are created and managed.
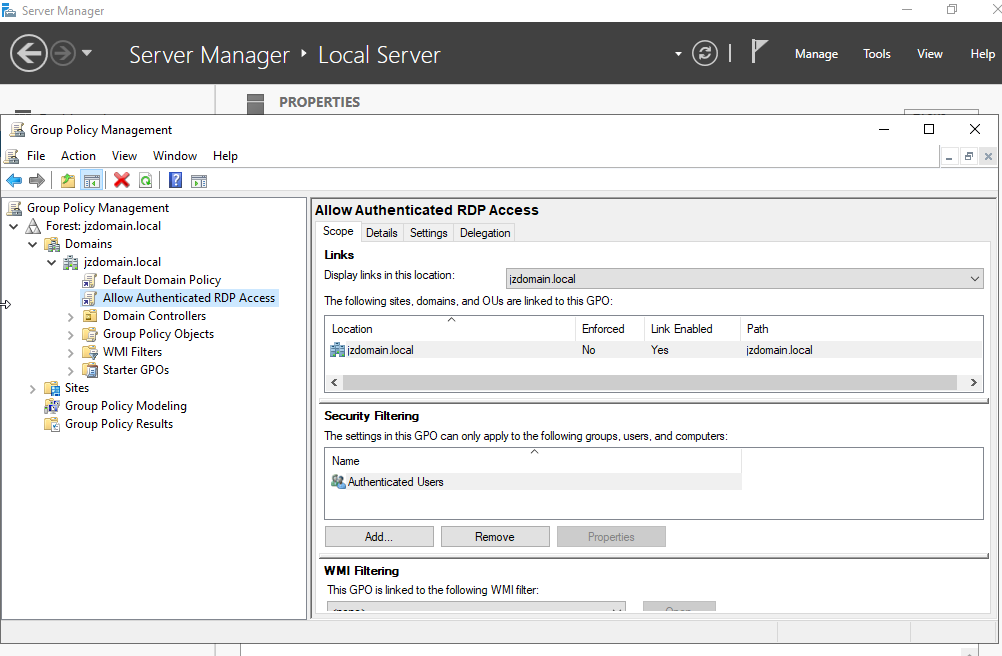
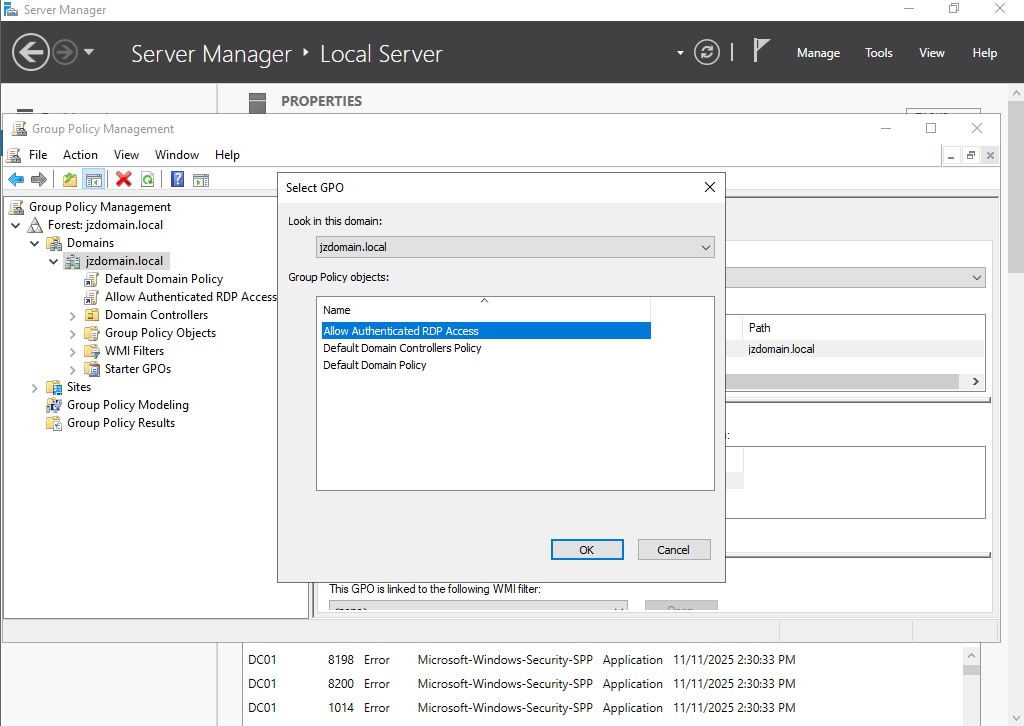
2. Create a New GPO
I created a new GPO with a clear name describing its purpose (for example, Remote Desktop Access GPO), and scoped it for the domain computers that should allow Remote Desktop.
Creating a dedicated GPO keeps the RDP configuration centralized and easy to maintain.
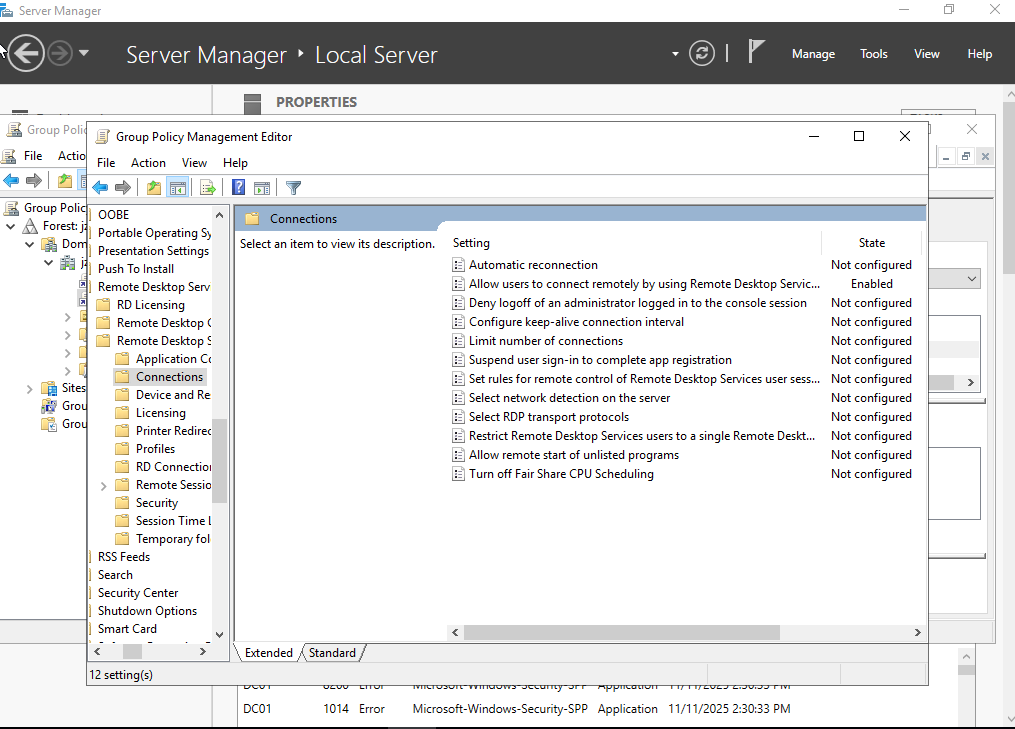
3. Enable Remote Desktop Access
Within the GPO, I enabled Remote Desktop so that any computer receiving this policy will have RDP turned on automatically. Configuring it through Group Policy ensures a consistent setup on every domain-joined machine instead of relying on local manual changes.
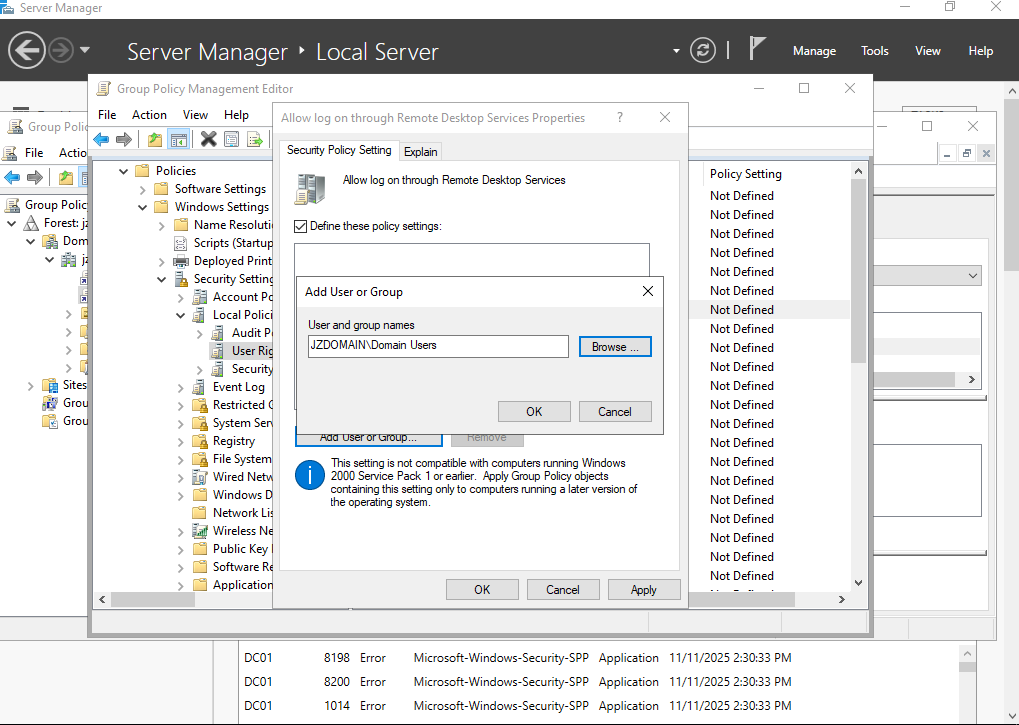
4. Allow Only Authenticated Users to Access RDP
I restricted RDP access to authenticated domain users and, if needed, specific security groups. This prevents unknown or non-domain accounts from connecting, limiting remote access to trusted identities and devices joined to the domain.
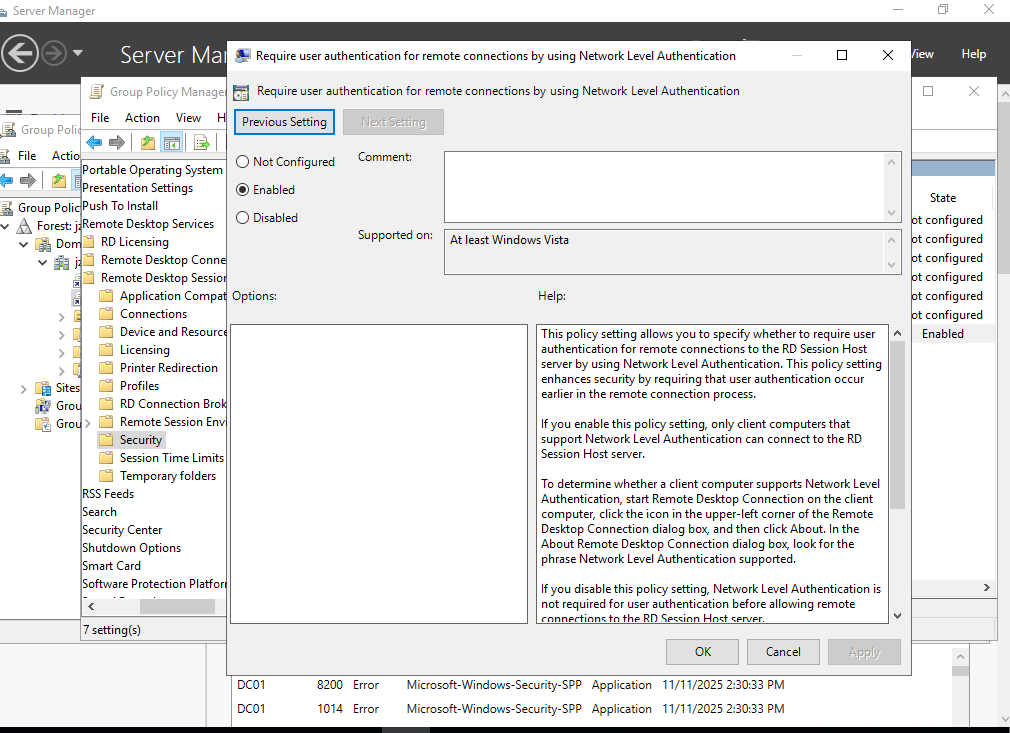
5. Enable Network Level Authentication (NLA)
I enabled Network Level Authentication (NLA) to add an extra layer of security. With NLA, users must authenticate before a full Remote Desktop session is created, which reduces the attack surface and helps protect the system from unauthorized connection attempts.
6. Link the GPO to All Domain Computers
I linked the GPO at the domain or OU level so it applies to the correct set of computers (desktops, laptops, and servers) that should allow RDP access.
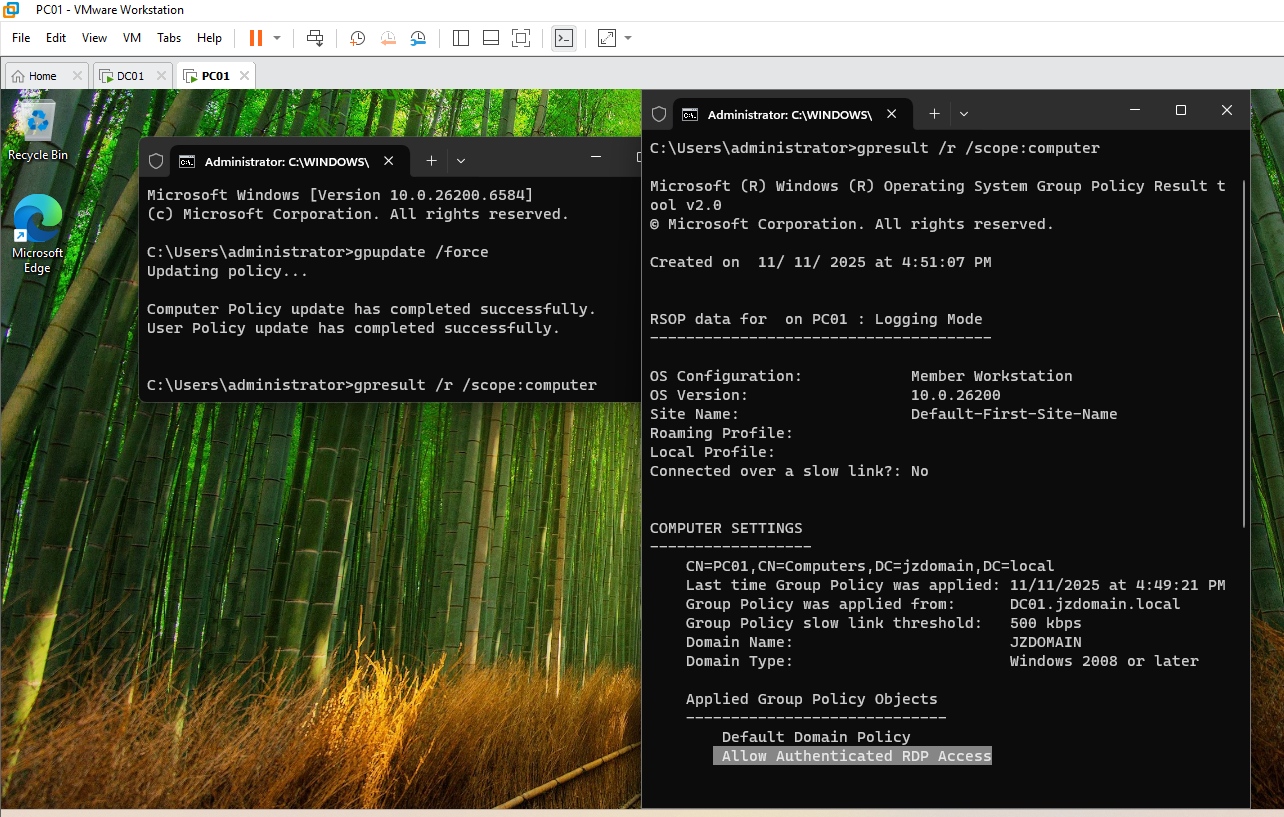
7. Force the GPO to Apply
On a domain-joined computer, I forced a Group Policy refresh so the new RDP settings would apply immediately instead of waiting for the normal background update cycle:
gpupdate /force
After the update completed, I tested RDP access and confirmed that only authenticated domain accounts could successfully connect.
Summary
This GPO standardizes Remote Desktop configuration across the domain and secures it by:
- Enabling RDP only where needed
- Restricting access to authenticated domain users and groups
- Requiring Network Level Authentication for all remote sessions
- Applying the same policy consistently to all scoped domain devices